USA. Its propaganda was always slicker than the Nazi’s. It has decades more experience in terrorism than Al Qaeda. And now it comes first in the world for state mass surveillance too.
Amid the storm of revelations about the Five Eyes mass surveillance system that NSA whistle-blower Edward Snowden blew wide open, Snoopman finds it curious that the US National Security Agency still promotes its creation myth: that it was formed to prevent another ‘Pearl Harbor’.
He concludes that if the NSA staff and its outsourced contractors would simply make a trip to the Library of Congress to read well-researched books such as Day of Deceit: The Truth about FDR and Pearl Harbor, they would realize that the Five Eyes spy network is one of three critical components of a totalitarian state apparatus.
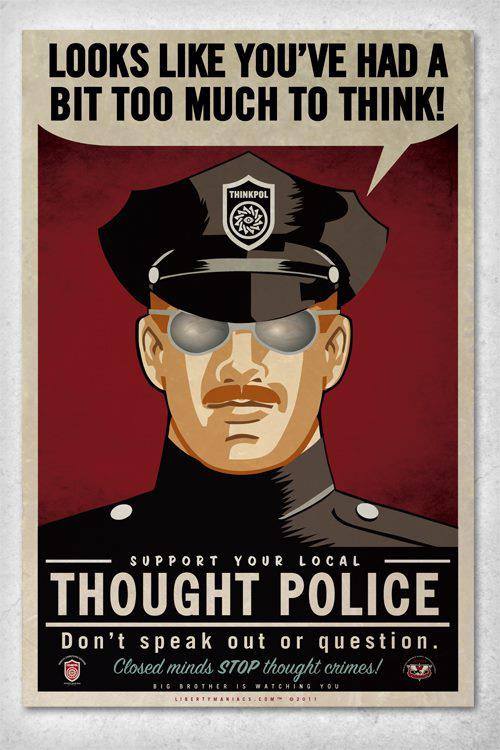
Indeed, propaganda, terrorism and mass surveillance were the very same components critical to the power of the totalitarian super-state, Oceania, depicted in George Orwell’s dystopian novel Nineteen Eighty-four. In this fully referenced feature, Snoopman goes beyond the Bubble Gum TV News History of the United States to investigate how and why this has happened.
By Snoopman (Last updated 3 June 2014; Posted on Scoop News 18 September 2014)
USA, NSA & the Construction of a Totalitarian Super-State
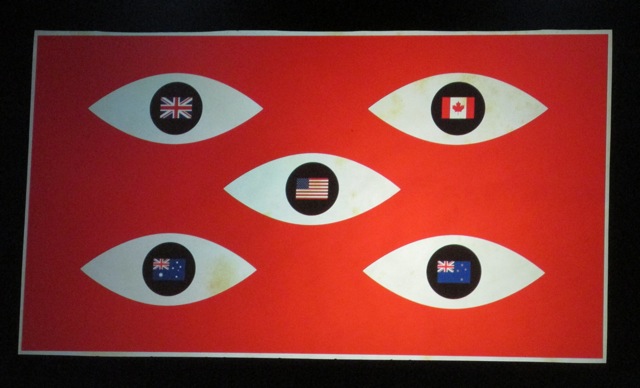
The Echelon global mass surveillance network, that is comprised of the ‘Five Eyes’ spy partners – the United States, the United Kingdom, Canada, Australia and New Zealand – poses a bona fide threat to the ideal of free and open societies.
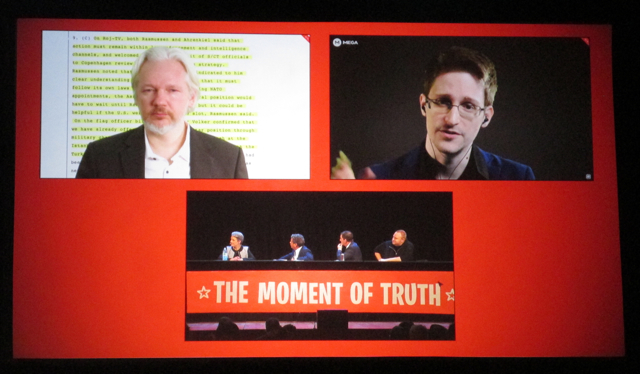
Thanks to US National Security Agency’s (NSA) highly-skilled cyber-operative turned whistle-blower Edward Snowden, the world has been able to learn that these five Anglo-Saxon countries have constructed an important technological component of a totalitarian system.[1]
Indeed, the ‘Five Eyes’ spy network is in breach of the United Nations’ Universal Declaration of Human Rights of 1948. Article 12 of this declaration, to which all Echelon ‘Five Eyes’ spy partners are signatories, states: “No one shall be subjected to arbitrary interference with his privacy, family, home or correspondence…”[2]
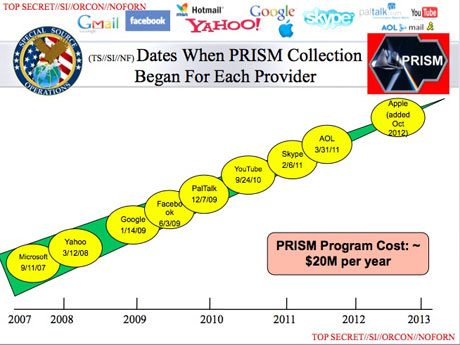
Snowden’s whistle-blowing has revealed the extensiveness of the Five Eyes network’s penetration into the world’s digital communications. The leaked NSA documents show the US spy agency has developed a decryption program called “BULLRUN”, that can “exploit” encrypted internet data.[3] All Five Eyes spy partners use BULLRUN. The NSA’s UK counterpart, the GCHQ, bragged in one document that it had designed “new access opportunities” into Google’s systems and had been seeking to do the same with other major internet firms such as Microsoft’s Hotmail, Yahoo, and Facebook.[4] However, the world also learned in early June 2013 that through the PRISM program, the NSA can directly access the systems of Microsoft, Hotmail, Skype, Apple, Google, YouTube, Gmail, Facebook and Yahoo.[5]
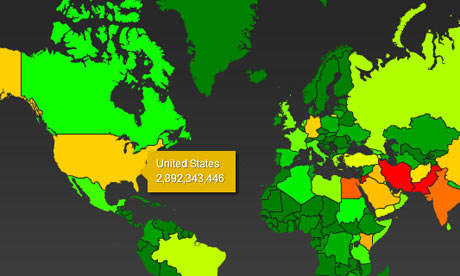
Additionally, intelligence analysts around the world can access practically any digital communications through another program called X-KEYSCORE, as Snowden’s ‘go to newspaper’, The Guardian revealed in late July 2013.[6] According to the NSA’s leaked documents, this “widest reaching” program can access real-time communications, and digital histories of a person’s internet activity such as web searches, the content of emails and social media communications, and the metadata to help refine searches of people’s networks. All the operator needs is an email address or some other contact detail, according to Edward Snowden. Furthermore, the Five Eyes global surveillance system can snoop on people’s conversations, activities and movements by accessing cellphones and computer microphones, even when they are switched off![7]

While the collection of meta-data has been acknowledged by the Five Eyes nation’s leaders and head spooks, this collection of ‘data behind the data’ – such as phone numbers, IP addresses, email addresses, contact lists and websites visited – is also a breach of the Universal Declaration of Human Rights. That is because it still qualifies as arbitrary interference of a person’s right to privacy, family, home and private communications. By being able to snoop on the mass populaces’ communications’ data sets, the Five Eyes spy agencies gain an invasive picture of who people know, the sites they visit and the organizations they contact. This secretive access is nothing but arbitrary. In other words, the state gains the power to data mine, build digital pictures of people’s lives and build new maps of the world to exploit. The collection of metadata, therefore, is a breach of the right to freedom of association.[8] That is why the Five Eyes’ governments are at pains to deny or refuse to confirm that their global surveillance system is a mass one.
Instead, the Five Eyes leaders claim it is ‘targeted’ to catch suspected criminals. This lie is akin to the state saying it is only interested in catching snapper, while exploiting every trawling technology available, every waiver of marine reserve provisions and routinely flouting international treaties, charters and even ecological science. In the process, this metaphorical fishing fleet catches every other hapless species of fish, by surreptitiously transferring everyone to a virtual ‘privacy extinction list’. The intention is to mine data for commercial exploitation, not only of rival countries and their transnational corporations, in order to gain advantages in trade negotiations. But also, through an alliance with corporate partners, codenamed ASPHALT, the NSA planned to gather everything. The purpose, as I shall show, is to ensure that the dominant capitalist coalitions, or oligarchies, that sit atop of the Five Eyes countries gain a decisive edge in a global game of economic warfare, military dominance and political intrigue.
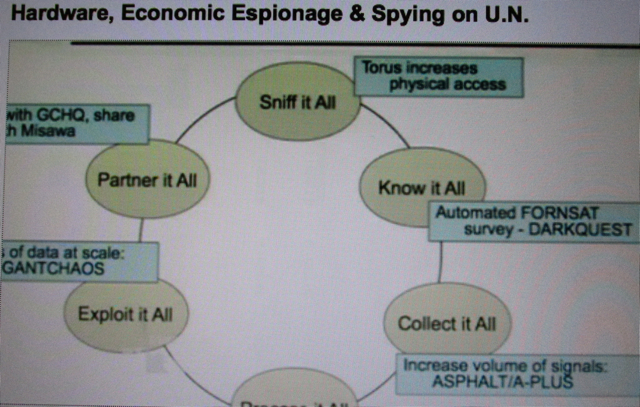
The NSA’s British counterpart, the Government Communications Headquarters (GCHQ), also has a “collect it all” alliance with major companies under the codename TARMAC. The symbolism inherent to the codenames, ASPHALT and TARMAC, is particularly potent when the adage ‘All roads lead to Rome’ is recalled. It becomes truly spooky when it’s remembered that the Roman Empire’s insatiable appetite for making war was facilitated by road building and it’s acknowledged that America and Britain head a transnational corporate empire.

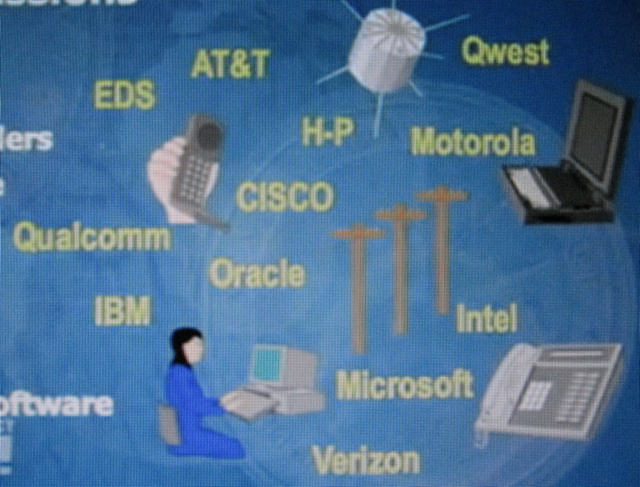
The NSA brags that it has strategic partnerships with over 80 global corporations, including: AT&T, IBM, Motorola, Microsoft, Hewlett Packard (HP), Intel, Dell, Verizon, Cisco, EDS (now HP), Qwest (now part of Centurylink), Oracle, Qualcomm, Google, YouTube, Facebook, Microsoft, Skype, Apple, Twitter, Yahoo, PalTalk, AOL, Booz Allen Hamilton, Northrop Grumman, and Science Applications International Corporation (SAIC).[9]The Guardian revealed that three transnational telecommunications companies, Vodafone, Verizon and BT, had also cooperated with the GCHQ to access their fibre-optic networks, under a program codenamed TEMPORA.[10]
To date, the news media has failed to highlight this breach to the Universal Declaration of Human Rights. Furthermore, this human rights provision was written as a protection for citizens against the fascism that had occurred under Hitler, Mussolini and Stalin.
Pinstripe fascists and the mass surveillance state
Perhaps if it was by now common knowledge that one of the NSA’s corporate partners, IBM (International Business Machines), made the Nazi’s twelve year reign technically possible and more horrific than it would have otherwise been, the world would fully realize that an important technological component of fascism has been implemented. IBM not only supplied their computing machines and punch card systems to the Nazis, so that Jewish, gypsy and gay people could be efficiently rounded up, transported across Europe and worked to death.
As Edwin Black proves compellingly in his book, IBM and the Holocaust, the solutions company also maintained its own leased machines, constantly redesigned the punch cards in full knowledge of their customers’ purposes, and collected on the profits, as per arrangement, after World War II and the Final Solution.[11] In other words, IBM’s punch card machines were an efficient mass surveillance tool for storing, organizing and communicating metadata to prosecute the Holocaust.
IBM’s critical material support of the Nazi’s prior to and throughout World War II was not an isolated case. Some of America’s other iconic industrial corporations supplied the fascist regime with patents, technologies and materials, in order to ultimately gain from the destruction of the Third Reich’s war machine. These corporations included: Rockefeller’s Standard Oil cartel, General Motors, General Electric, DuPont, Dow Chemical and International Telephone and Telegraph (IT&T). An American Fraternity also deliberately financed the Nazis, as William Engdahl demonstrates in Gods of Money; Charles Higham shows in Trading with the Enemy: The Nazi-American Money Plot 1933-1949, Guido Giacomo Preparata proves in Conjuring Hitler; and Anthony Sutton argues compellingly in Wall Street and the Rise of Hitler. The Nazi-financing Wall Street banks included: the Chase National Bank (now JP Morgan Chase); the Schroeder-Rockefeller Company; the Manhattan Bank; the National City Bank of New York (now Citibank); the New York Trust Company; V. A. Harriman & Co. and Dillon & Read.
Without these technologies, co-investments, and raw materials supplied by American industrial and banking corporations, the Nazis could not have: motorized their army; flown bombers and fighter planes; manufactured explosives on an epic scale; and exploited information to make the inevitable Holocaust as horrific as it became. This collaboration between Wall Street banking and industrial cartels and the Nazis occurred with the complicity and active participation of government actors across the state apparatus of Britain, America and Germany, with ‘neutral’ countries such as Switzerland, Sweden, Argentina, Brazil and Panama playing vital roles, as the above mentioned authors show.
It is also pertinent to note the expansion of the NSA’s spying powers were signed off by President George W. Bush, whose administration warped the law to deem mass surveillance of the American population ‘legal’, as is made clear in the documentary United States of Secrets.[12] Pertinent, because George W. Bush’s grandfather, Prescott Bush, who became a wealthy industrialist manufacturing armaments during World War II, was also a director at Union Banking Corporation, a Wall Street bank that moved funds back and forth between the United States and Germany for Nazi financier and steel magnate Fritz Thyssen. Indeed, US family dynasties such as the Bushes, the Rockefeller’s, the Harriman’s, and the DuPont’s were not only a part of the Nazi Nexus for profit. As an American oligarchy, they conspired to head the world’s dominant military and financial empire, centred around the control of oil.[13]
‘Uncrackable’ History of US-sponsored Terrorism: From WWII to the Shock Doctrine
A major justification for the Five Eyes’ state spying apparatus is countering terrorism. Indeed, in the PBS documentary United States of Secrets, about NSA’s mass surveillance on the US population since the terror attacks of September 11 2001 or 9/11, it is claimed that the National Security Agency was formed after World War II so that the United States is never surprised again with another Pearl Harbor-type attack.[14]
Contrary to the official story advanced today by the U.S. National Security Agency, key insiders of President Delano Roosevelt’s Administration were not taken by surprise, including Roosevelt himself, as Robert Stinnett makes clear in his book Day of Deceit: The Truth about FDR and Pearl Harbor.[15] During 17 years of military archival research, Stinnett found that two weeks before the attack, Washington had issued a ‘Vacant Sea’ order for the North Pacific, to reduce the chances of the Japanese naval fleet being sighted by military and merchant ships. Washington had also ordered the newest US warships – twenty-one in all, including two aircraft carriers – out of Pearl Harbor. The United States Navy and Army cryptographers had cracked the codes of Japanese diplomatic and military encrypted messages since December 1940. On that basis, a secret inner circle around president Roosevelt had conspired with the British and Dutch governments to cut off crucial supplies of oil, steel and aviation lubricants to Japan in order to provoke the Imperial Government of Japan to attack Pearl Harbor. Despite what the NSA still claims, Japanese diplomatic messages did contain military information and the Japanese fleet did not travel under radio silence, because they did not know their communications had been decrypted.
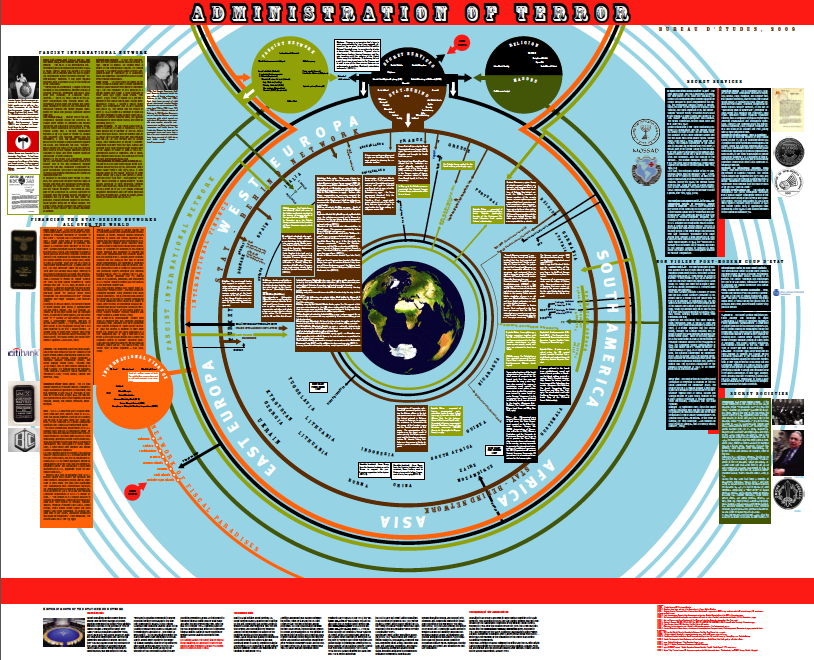
In their accounts of the post-World War II order, journalists such as John Pilger and Naomi Klein, and documentary filmmaker Eugene Jarecki, along with US foreign policy critic Noam Chomsky, have shown that the US-NATO Alliance has routinely conducted acts of terror.[16] These Black Operations, as they are called, have occurred in over 50 countries and were often conducted to topple democratic socialist governments or communist states in Europe, Central and South America, South East Asia, the Middle East and Africa. After World War II, the Atlantic Alliance covertly formed a secret ‘stay behind’ army by recruiting fascists, including former Nazis, to conduct terrorism operations codenamed ‘Gladio’ (Latin for Roman sword). Operation Gladio was a low-grade war that exploited a “Strategy of Tension” designed to frighten the mass populaces of Europe and thereby shift the political gravity to the ‘right’.[17] These clandestine ‘false flag’ operations were continued by all NATO countries after its formation in 1949, and were carried out by their intelligence services, militaries, and paramilitaries, with dominant participation from the Anglo-American membership of NATO, as Madhi Darius Nazemroaya reports in his book The Globalization of NATO.
The bombings of trains, planes, automobiles, buses, and buildings conducted under Operation ‘Gladio’ were ‘false flag’ operations. In conventional warfare, a belligerent state conducting a ‘false flag’ terror operation uses another country’s ‘flag’ with the intention to frame the enemy as the perpetrator (or covert acts of provocation to lure an enemy to make an overt attack, while denying the provocation).[18] By blaming ‘left’ wing groups for the carnage of Operation Gladio, key insiders that involved the CIA, MI6 and the Coordination and Planning Committee (CPC) of NATO’s Supreme Headquarters Allied Powers Europe (SHAPE), could manipulate people with subtle propaganda that a ‘free world’ equated with capitalism. (SEE full resolution version here: Terror Network Chart)
Prior to the highly public exposure of Operation Gladio in 1990, and numerous state investigations, the US-NATO Alliance added a new modus operandi by funding, training and resourcing groups in jurisdictions not under their control, to create what appear to be grassroots uprisings in order to topple ‘insubordinate’ governments. Such ‘uprisings’ as the Arab Spring have been called ‘color revolutions’ because a color is chosen for flags, banners and clothing to manipulate perceptions and emotions by manufacturing the image of widespread solidarity, as Thierry Meyssan has identified.[19] This style of coup is made to appear as though it started in the ‘streets’ through a popular uprising to rid an oppressed people of an autocratic leader or government. The US Congress gives AID funds through ‘democracy building’ programs. The Western mainstream media can be counted on to report a Bubble Gum TV News version of events that fails to challenge these US-NATO clandestine operations. The events themselves and their distorted reconstructions in the Bubble Gum News are written by black satirists with a taste for the fascist aesthetic of violence.
Indeed, Eugene Jarecki’s Sundance Film Festival Grand Jury Prize-winning documentary Why We Fight compellingly shows that America fights wars to make the world secure for its corporations. This covert strategy, identified by Klein as the ‘Shock Doctrine’, was crucial to roll-out and deepen the incursion of ‘free market economic shock treatments’, where states refused to submit to other acts of coercion, including engineered financial crises.
Therefore, the Deep State is a secret political system that is comprised of networks of criminal players from the Overworld Cabal who run the machinary of power as a Shadow Government, parallel to the visible government and public state, according to its own compass regardless of who is formally in power. This Overworld Cabal or Shadow Government are the Overlords, the architects and the paymasters who orchestrate, plan, and fund the Deep State system, power crimes, and exploit the speed of fast-moving deep events that re-set the trajectories of the public state, whole societies and create copies of reality, in cahoots with associates from the Underworld Force of the Deep State. This Underworld Force is comprised of operational level criminal actors embedded in intelligence agencies, secret services, special forces, mafias, gangs and mercenaries.
Forward Engineering 1984: A Slicker, Snazzier, Faster, More ‘Fun’ Totalitarian State

Too few today recognize this totalitarian state is in an advanced stage of construction around them because it does not look like the Orwellian world of Nineteen Eighty-four. In George Orwell’s dystopian novel, the power of the totalitarian super-state, Oceania, relies on mass surveillance, propaganda, and terrorism (in the form of torture administered to dissidents deemed to be ‘thoughtcriminals’). Oceania is engaged in a perpetual war with either one of two rival super-states, Eurasia and Eastasia, at various times. A banned book, The Theory and Practice of Oligarchical Collectivism, reveals that the purpose of war is to waste the resources and productive energy of society, so that the mass populaces never rise above toil and poverty to challenge an unseen oligarchy.
Meanwhile, in the real world, American journalist Chris Hedges has reported a corporate totalitarian core thrives inside a fictitious democratic shell. Recent studies show that a Transnational Capitalist Class is steering capitalism by means of highly-networked corporate board directorships and ownership.[20] This corporate totalitarian core, comprising just 147 corporations, is spreading outward from America. In essence, a corporatized totalitarianism is driving the construction of a worldwide technocratic system. A technocracy is a totalitarian system of government administered by scientists, engineers and technicians. Key insiders manage the technocratic system in service of super-rich people, or oligarchs, who use their vast economic resources to steer the trajectory of whole societies.
In this section, I sketch why and how this happened.
In the early 1970’s, elite planners that were part of the North Atlantic capitalist class met to discuss threats to their power under the auspices of the “1980’s Project;” the goal of which was to reconfigure control of the planet.[21] Central to this project was the deployment of neo-liberal ideology under the rubric of ‘free market reforms’.[22] Despite the ideological claim of ‘prosperity for all’ used to promote the deployment of ‘free market economic shock treatments’, the intention was to reduce the material wealth of mass populaces so that they would be less able to assert their political independence. The purpose was to hinder the efforts of the ‘disobedient’ and thereby counter the cultural movements that had emerged in the 1960s, as well as the developmental demands of ‘Third World’ countries that sought to be decolonized.[23]
To this end, in April 1972, the chairman of the Council on Foreign Relations, David Rockefeller, presented his idea of a new alliance between the wealthy and politically connected of America, Europe and Japan to a secretive global policy-shaping group called the Bilderberg Group, which convened in Knokke, Belgium. It’s difficult to overstate the role played by this oligarch. If there were a board game invented to make Monopoly obsolete, say Oligarchy, David Rockefeller would inspire a special oligarchic game-piece that looks, thinks and moves like an octopus, for he has been a prominent member of the Bilderberg Group since its first meeting in 1954. Editor-in-chief of the Voltaire Network, Thierry Meyssan, who has accessed the Bilderberg Group’s records for 1954 to 1966 (and numerous records pertaining to later years), stated the Group is a lobbying tool for the NATO Alliance, North Atlantic militarists that intend to be a secret world government.[24]

It had the credentials to be that, since it’s first chairman was Prince Bernard, a German aristocrat who served in the SS cavalry up until marrying into the Dutch royal family. The first Bilderberg meeting appeared to be intended to promote ‘free-market’ capitalism, against a background of communism and socialism. However, the real organizing power behind the Bilderberg Group were the secret services of NATO and their purpose was to escalate the Cold War. The attendees were selected to influence their respective governments and opinion-makers to support the NATO Alliance worldview, that soon went as far as to assert there was a “communist world conspiracy”. In effect, key insiders had plotted a Psy-Op (or Psychological Operation) on the attendees. As opinion-makers themselves, the participants were expected to disseminate the ruling cliques’ ideological construct in their home countries, so that the mass populaces’ attention would be diverted to restrictions on freedom in places such as Eastern Bloc states, while failing to notice the incremental curtailment of rights at home. It was through the NATO Alliance, and its top secret ‘false flag’ Black Ops, Gladio, that the US was able to continue to use terrorism to destabilize governments that opposed submission to the will of the world’s most powerful ‘pinstriped’-suited oligarchs: the North Atlantic capitalist class.[25]

In July 1972, David Rockefeller hosted 250 oligarchs and elites at his country estate in Pocantico Hills, Hudson Valley, New York. At the time, he was chairman of Chase Manhattan Bank’s board of directors, because he owned a controlling stake, and since this meant Chase owned a significant share in the New York Federal Reserve Bank, Rockefeller was also a Class A director on the New York Fed’s board.[26] David Rockefeller was also chairman of a New York-based global policy-shaping think-tank, the Council on Foreign Relations (CFR). At the Pocantico Hills meeting, Rockefeller and his posh guests formed a new global-policy shaping think tank called the Trilateral Commission. This new global-policy shaping group was designed to formulate policies, strategies and tactics to further what The Economist later called a “counterrevolution”.[27]
This counter-revolution, amply detailed in The Shock Doctrine, which sought to establish a ‘new world economic order’ between America, Europe and Japan, was designed to usurp the sovereignty of national governments through incremental changes rather than the frontal assaults of the past.[28] By joining forces with oligarchs from Japan, the Trilateral Commission’s task was to drive the roll-out of the “1980’s Project”, which included globalizing neo-liberal ideology, in order create a worldwide technocratic system.[29] At face value, a technocracy suggests a benign economic system that allocates energy and resources equitably through quotas, rather than through capitalism’s current price system.
In 1973, David Rockefeller’s brother, John D. III, published a book called The Second American Revolution, in which he argued for a radical transference of state “functions and responsibilities” to private interests.[33] The following year, Columbia University academic Richard Gardner published an article called Hard Road to World Order in the Council on Foreign Relations magazine Foreign Affairs, in which he wrote that the building of a new world economic order would require “an end run around national sovereignty, eroding it piece by piece” because “the old-fashioned frontal assault” had become less effective.[34] Gardner’s think-piece expressed the same sentiment as that espoused by another Columbia University professor Zbigniew Brzezinski, who stated in his 1969 book called Between Two Ages: America’s Role in the Technetronic Era that “[i]nternational banks and multinational corporations are acting and planning in terms that are far in advance of the political concepts of the national-state”.[35] Brzezinski, who later co-founded the Trilateral Commission with David Rockefeller, stated that “political innovation” was unlikely to occur with open debate, but rather through covert incrementalism. Gardner, who had been a member of president Nixon’s Commission on International Trade and Investment Policy, argued that the construction of a new world economic order would appear as a “great ‘booming, buzzing confusion.” Indeed, such confusion was the linchpin of neo-liberal ideology.
As US under-secretary of State of Economic Affairs, George Ball, implied in his presentation entitled “Internationalization of Business” at the 1968 Bilderberg meeting at Mont Tremblant Canada, the major obstacle to a neo-colonial world empire, or ‘world company’ (as he worded it), were nation states committed to the common welfare of their respective citizenries. [36] Therefore, a cover story that promoted freedom and prosperity through economic growth, or a consumerist-investor cult, was needed to hide the gradual deployment of a technocratic world system. That cover story was neo-liberal ideology, which was sold universally to the world’s public with the made-for-media catch-phrase – the ‘trickle-down effect.’ This mocking promise was predicated on the notion that the rich were needed in order for society to prosper, without emphasizing that the rich would control the tap and make sure it never more than trickled.
The key insiders of the North Atlantic capitalist class that were behind the ‘1980’s Project’ – the blueprint for transforming the world with ‘free market’ economic frameworks – were mocking the world because they covertly controlled capitalism[37]. These key insiders, therefore, knew that capitalism is a private political system that uses economic means to control society by limiting people’s access to land, as Frances Hutchinson (1998) argued in, What Everyone Wants to Know About Money and Jonathan Nitzan and Shimson Bichler presented in Capital as Power. This political control is primarily achieved through a deliberate scarcity of cash and an abundance of credit/debt, as Michael Rowbotham (1998) showed in his book, The Grip of Death: A Study in Modern Money, Debt Slavery and Destructive Economics. This scarcity of debt-free cash is controlled by the oligarchic bankers, such as David Rockefeller, because it is the wealthiest that own the major banking cartels that, in turn, have come to control the governments of the world through coercion. By gaining control of credit creation over several centuries, through military, economic and psychological warfare, dynastic banking families have captured states that are forced to borrow to meet revenue shortfalls.
As with dripping taps, the amount and interval of ‘liquid’ credit would be regulated by the market’s ‘Invisible Hand’, which was a euphemism for an oligarchy and their army of unseen professionals, who have constructed a Worldwide Financial-secrecy Haven Complex. Oligarchs are super-rich people who use their enormous wealth to influence the politics of society. At the superficial level, news outlets manufactured the idea that in a ‘free market’ system, where government intervention was prevented, the Invisible Hand would price goods and services efficiently through rigorous competition. However, the highly-networked North Atlantic capitalist class used private political mechanisms to ensure that wealth accumulated upward, so that there was only just enough income trickling-down to avert rebellion. Meanwhile, fees for ‘public’ services increased, even as the universal tax system remained in place.
A Wall Street-Washington-City-of-London Complex has been ruthlessly successful at loosening financial regulation, down-sizing state sector services and buying up state infrastructure at fire-sale prices.[38] This Complex, comprised mainly of key bankers, accountants and lawyers in Gotham and its fraternal dark twin, the City of London, along with key insiders in Washington at such illuminated institutions as The World Bank Group and the IMF (International Monetary Fund), exploits the crises they cause as mechanisms of change. The spread of ‘free market’ capitalism and the use of military violence is inextricably linked, as Naomi Klein made clear in her book The Shock Doctrine: The Rise of Disaster Capitalism.
The Shock Doctrine is the denied part of the global neo-colonial project. During the field-testing stage of ‘free markets’ in the mid-1960s to mid-1970s, US-backed terrorism was required to clear opposition for the ‘free market economic shock treatments’ that followed. Five countries – Brazil, Indonesia, Chile, Uruguay and Argentina – pursued a developmentalist economic framework and were all subjected to military juntas and/or CIA-backed coups. In the Chilean case, General Augusto Pinochet’s CIA-backed coup of September 11 1973 was ordered by US National Security Adviser Henry Kissinger, who viewed president Salvador Allende’s socialist government as a “contagious example”, because he had nationalized key infrastructure and resources, owned by American and Chilean corporations.[39] But, these ‘developmentalist’ countries were not the only ones in need of ‘free market’ discipline.

Henry Kissinger had already conspired to foment a bolder shock treatment that would reverberate around the world. Together with his close accomplices, David Rockefeller and Zbigniew Brzezinski, Kissinger attended the May 1973 Bilderberg meeting at the island resort of Saltsjöbaden, owned by the Swedish Wallenberg banking dynasty, to discuss a plot to trigger oil price shocks, which would return enormous profits for key banks and the oil majors, including Rockefeller’s Chase Manhattan Bank and the Standard Oil cartel. (These shocks would also reinvigorate the indebted US dollar, through which oil was traded universally).[40] The Bilderberger Nexus Oil Price Shocks of 1973-1974 were anticipated to cause a 400% hike in oil prices, according to the 1973 Saltsjöbaden Bilderberg Meeting Report. The Oil Price Shocks caused an inflationary spiral in the cost of energy and transportation, that in six years to the end of 1979 had risen by 1300%, according to William Engdahl in A Century of War.
In keeping with the anti-competitive behaviour of cartels, Henry Kissinger explained at one session of a US Federal Staff Energy Seminar, (which ran for four years), that the US was seeking to “create a world price for oil”, according to former US Air Force Colonel L. Fletcher Prouty. This ‘energy crisis’ served as a pretext for the Wall Street-Washington-City of London Complex to increase the cost of credit to 20% (amid runaway inflation), and when combined with the underlying Bilderberg Nexus-induced economic crisis, a world debt crisis emerged. Thus, the ‘deep state’ oil price shocks laid the groundwork for further ‘free market economic shock therapies’, which were themselves mechanisms of coercion, because all governments and sectors of society were thrown further into crisis. Everyone suffered, except key insiders, who became richer and accumulated more political power.
9/11 and Full Spectrum Dominance
Investigators such as Peter Dale Scott, Webster Griffin Tarpley, Mike Ruppert and Kevin Ryan have gone further than the high profile critics of US foreign policy such as Chomsky, Klein, Jarecki and Pilger, who have already been cited. Scott, Tarpley, Ruppert and Ryan say that deep state criminals periodically conduct deep state events, or “re-adjustments” to extend the power of the transnational capitalist class.[41] Their studies are part of citizens’-initiated 9/11 investigations that argue that the official core claims are implausible. These citizens’-initiated 9/11 investigations vary according to expertise, such as technical studies of: the near-free fall speed collapses of the three towers that imploded at the World Trade Center; tracking the four hijacked flights; and presenting the more likely suspects.[42]

Professional group Architects and Engineers for 9/11 Truth (AE911Truth), who together represent over 25,000 years worth of experience, point out that only three steel-reinforced concrete towers have ever been officially claimed to have collapsed by cause of fire. Remarkably, all three of these instances occurred on the same day, September 11 2001. AE911Truth assert that the World Trade Center Twin Towers, and Building 7 (WTC 7), which was not hit by a plane, could not have collapsed due to office fires.[43] Indeed, the BBC announced the collapse of Building 7, prior to its failure. One of the British broadcaster’s reporters was filmed with the 47-storey tower still standing in the background of her live shot as she broke the news of its collapse!
As Consensus 9/11 report, numerous witnesses, including firemen, stated they were waiting for WTC Building 7 to collapse, despite the official report of the U.S. National Institute of Standards and Technology (NIST) claiming the structure failed due to fire. To be clear, architects, engineers and building demolition experts say that it takes weeks, if not months, to prepare a building so that it can collapse in on its own footprint, as happened with all three World Trade Center towers. WTC7 building leaseholder Larry Silverstein related in a PBS documentary America Rebuilds that a fire department commander called him the afternoon of September 11 to tell him that he had doubts that “they were gonna be able to contain the fire”. Silverstein claims he said “maybe the smartest thing to do is pull it.” The phrase “pull it” is demolition industry lingo for collapsing a building by controlled demolition.
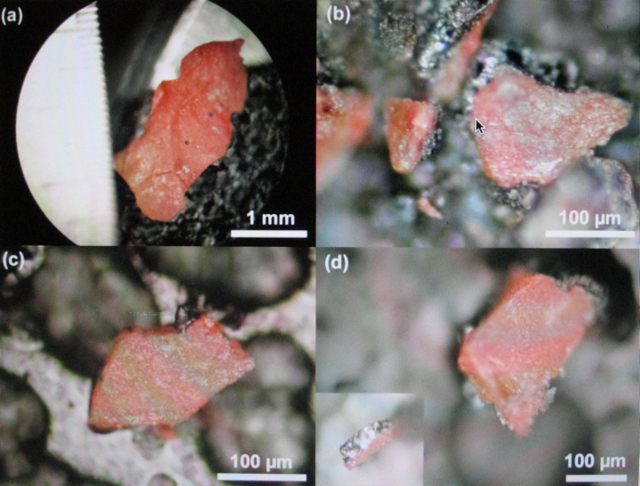
The latest tests of dust samples saved from the symbolically named ‘Ground Zero’ show traces of nano-thermite explosives.(See: Active Thermite Science Paper) These chemical traces strongly corroborate the theory that demolition industry explosives were pre-planted in the towers and explain why all three towers can be clearly seen collapsing at near free-fall speeds.[44] Such collapses are impossible without prior cutting of steel and concrete beams, so that the explosives can ‘lift’ the structures sideways, and make them implode in precise, computer-controlled sequences, as they fall.
The picture (above) of the South Tower (or World Trade Center 2) shows that as it begins to collapse, the top section falls asymmetrically, that is, it topples at a uneven angle. This image alone refutes the possibility of a symmetrical “pancake” implosion, wherein the mass of floors were deemed officially to have fallen evenly on each of the successive floors below them as they failed instantaneously, yielding a chain reaction of collapse. Yet, once this collapse of World Trade Center 2 started, the rest of the tower imploded at near free-fall speed. Since this upper section fell unevenly, the floors below could not have collapsed in a uniform ‘pancake’ style implosion without the help of pre-planted demolitions explosives. It is therefore very telling that the North Tower (or World Trade Center 1) collapsed symmetrically at near free-fall speed too.
When it is remembered that the Twin Towers were identical in construction, and both imploded at near free-fall speeds, the give-away that the South Tower had pre-planted explosives to assist its collapse lays in the fact that its top section is clearly seen toppling rather than falling straight down. The smoke, or squibs, of such explosives can be seen ejecting ahead of the field of collapse, as marked by the red rectangles in the above photo. In short, symmetrical collapse is impossible as a result of asymmetrical damage. Unless, the black satirists who scripted the 9/11 terror attacks could make almost everyone suspend their disbelief in order that they would appreciate the special FX of the newest scariest B-Grade blockbuster movie, in which the laws of physics failed temporarily, so that the only three steel-reinforced towers to have ever collapsed due to office fires, could happen all in one infamous day! The 9/11 blockbuster script required the absence of forensic scrutiny, or a cover-up. (See: Active Thermite Science Paper)
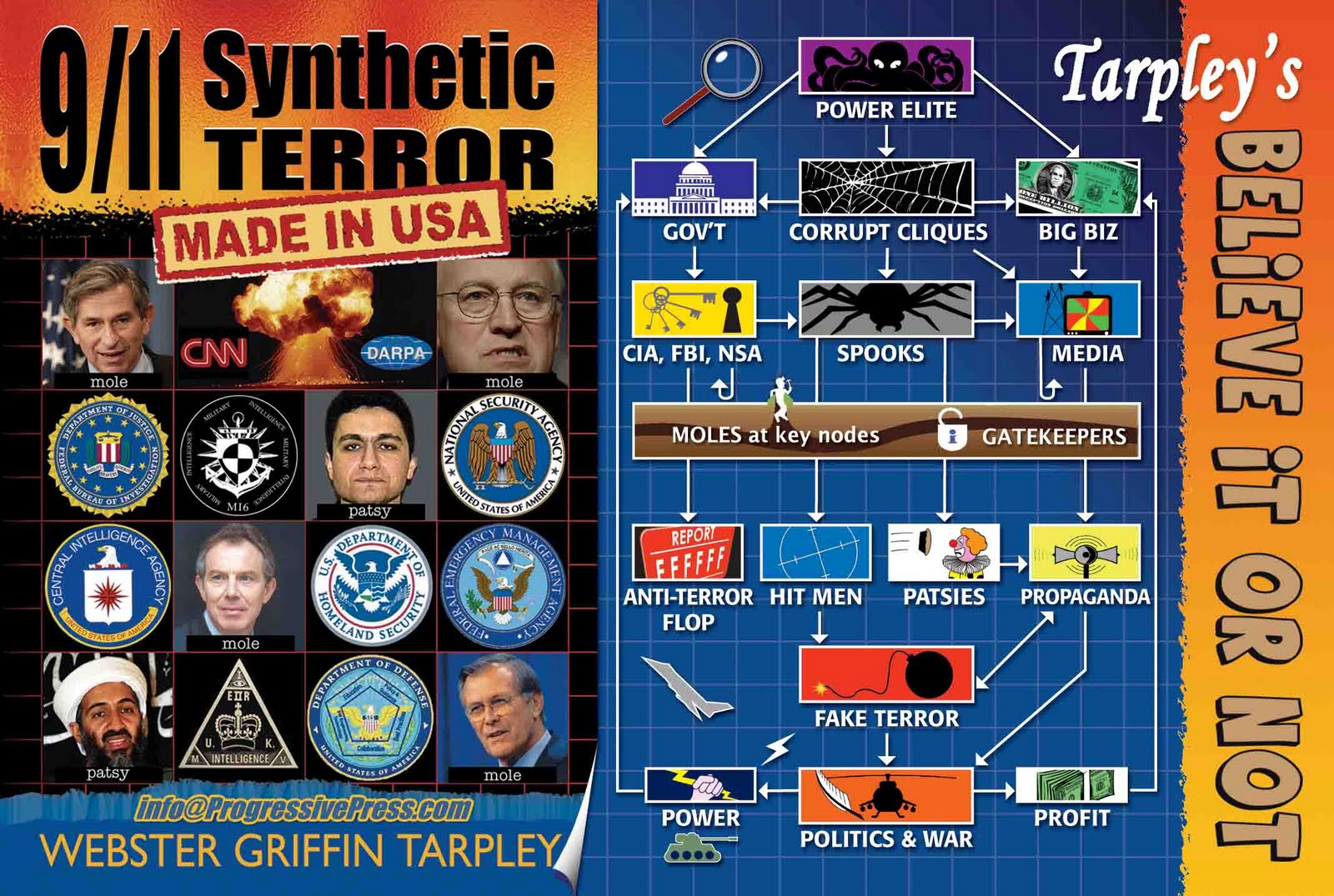
In his book 9/11 Revealed: The New Evidence, researcher Ian Henshall stated that there was a ‘wall’ created by 9/11 Commissioner Jamie Gorelick back in 1996 when she was at the US Justice Department, which meant that if the FBI was investigating cases and required information defined as intelligence (or INTEL), it put those FBI agents working in the INTEL section under the control of the CIA. This meant the INTEL FBI agents could not automatically share that information with criminal investigators at the FBI. This ‘wall’ also separated agents at the bureau from those at other departments including the State Department, the CIA and the Pentagon.[45] This separation was critical because as the author of 9/11 Synthetic Terror Webster Tarpley has found, there were up to 46 terror drills and war games that occurred on September 11 2001. These exercises provided the necessary cover for criminal actors within the state-corporate nexus to make the terror drills and war games go live.[46]
This is critical, because a now-defunct Washington-based think-tank called the Project for a New American Century (PNAC), argued the United States needed to transform its military to conform to the concurrent US military’s Joint Chiefs of Staff doctrine, ‘Full Spectrum Dominance’. This doctrine set a goal for the United States to dominate the world, whether on land, sea, air, space and cyberspace, by the year 2020, permanently (Emphasis added).[47] Indeed, it is highly suspect that in the immediate aftermath of 9/11, the NSA was ready to go ahead (by the end of October 2001), with new highly invasive mass surveillance technologies in a top secret project called ‘The Program’, and code-named ‘Stellar Wind’.[48] As the Snowden scooping litigator-turned-journalist Glenn Greenwald stated, the NSA has bragged it wants to “own the internet”.
A full year before 9/11, PNAC members had called for a ‘revolution in military affairs’, or the reconfiguration of American forces into smaller more mobile units, capable of exploiting new war-fighting technologies. Crucially, in a paper titled “Rebuilding America’s Defences”, this revolution, wrote the authors in September 2000, would take a long time, “absent some catastrophic and catalyzing event – like a new Pearl Harbor”.[49] Otherwise, the PNAC’s white paper, “Rebuilding America’s Defences” argued, the United States risked losing its sole super-power status if it was not seen to be fighting two major wars at once. PNAC members included many Washington technocrats that soon became members of President George Walker Bush’s administration: Richard Perle, Paul Wolfowitz, Dick Cheney, Donald Rumsfeld, L. Paul Bremer, and Robert Zoellick.[50] The intention of key Pentagon, armaments industrialists, banking and oil oligarchs, and Washington technocrats and politicos, is for the United States clique to be able to dictate the economic, political and military order of the planet, permanently, as William Engdahl makes clear in his book Full Spectrum Dominance: Totalitarian Democracy in the New World Order, and his earlier works, A Century of War and Gods of Money.
The sub-terrain connections of many PNAC members to what is known as the ‘deep state’, are revealed in Kevin Ryan’s intriguing book, Another Nineteen: Investigating 9/11 Suspects.[51] Kevin Ryan, presents a more likely list of top suspects that fit the picture of a far more realistic 9/11 narrative than the ridiculously over-simplified official story. These included key PNAC members: Vice-President Dick Cheney (2001-2009), Secretary of Defense, Donald Rumsfeld (2001-2006), and Richard Clark, Chairman of the Counter-terrorism Security Group (1992–2003); who together were part of a covert group during the Reagan presidency that planned and practiced Continuity of Government (COG) operations, or the takeover of the United States government in the event of an emergency. (Back in the Reagan era, this COG group included Oliver North, of Iran-Contra Affairs fame). Ryan shows that key insiders, that held top posts in the US state apparatus, had the means, motive and histories of ‘deep state’ activity to organize a coup d’état with their counterparts from the US corporate world, along with vital help from the Saudi and Pakistani regimes.
Among them, L. Paul Bremer, who was an assistant to Henry Kissinger (1972 -1976), of the 1973 CIA-backed Chilean coup fame. While he was managing director at Kissinger Associates in the 1990s, Bremer was also on the International Advisory Board of Japanese mining and machinery company, Komatsu, that had a joint venture with Dresser Industries (an oil services and intelligence front once owned by Averill Harriman, an American oligarch that willingly supported the Nazis, and for whom Prescott Bush Snr. worked for). In 1996, Komatsu-Dresser’s mining division patented a thermite demolitions device. Dresser Industries merged with Halliburton in 1998, while fellow PNAC member Dick Cheney was chairman and CEO of Halliburton. After leading the National Commission on Terrorism (1999-2000), Bremer worked for insurance conglomerate Marsh & McLennan, which occupied the exact eight floors of the North Tower that were struck by a jetliner resembling American Airlines Flight 11. Bremer, who was CEO of Marsh Political Risk Practice, survived because he was not at work at the time of the impact. This was unfortunate for the world, because he was then able to appear on NBC at lunchtime the same day to make a number of brazen claims in order to manipulate public perceptions. Bremer agreed with the male host that Osama bin Laden was the most likely suspect, and that maybe Iraq and Iran were involved too.
It is ironic that the female host introduced Bremer as a terrorism expert, a claim he quickly rebutted by saying his expertise was counter-terrorism. NBC could have introduced Bremer as a close associate of a known war criminal that is still at-large, Henry Kissinger, who ordered the CIA-backed Chilean coup of September 11 1973. (After all, Harper’s Magazine had published excerpts from Christopher Hitchens’ book The Trials of Henry Kissinger, in February and March 2001, in which the author argues that Kissinger used his position as US National Security Advisor, (and for a time as Secretary of State), to order genocidal scale killings in Bangladesh, Chile, Cyprus, East Timor and Indochina). NBC (and all the other major news outlets) should have been more skeptical.
Had NBC done its job properly tracking US ‘deep state’ actors, particularly after the publicity of US-sponsored terrorism in Operation Gladio, its audience would then have been more critical of Bremer’s audacious claim that “apparently we don’t have any forensic evidence”. This claim pre-empted any serious investigation of the 9/11 crimes scenes. It also worked as an encoded message to those in key leadership positions to take the hint of the leading expert on counter-terrorism that a crisis management narrative was being established. Bremer was subsequently chosen by fellow PNAC member Donald Rumsfeld to be the Iraq Occupation Governor in 2003, a post that he could be trusted with to serve big corporate interests, particularly as he and Rumsfeld had participated in a terrorism commission that failed to find that the US was a terrorism-sponsoring state when it published its report in 1999, as Kevin Ryan points out in his book, Another Nineteen.


Rumsfeld, who had planned with Cheney the takeover of the US government’s chains of command in the event of a national emergency since the Reagan era, stated the day before the 9/11 mass terror events that $2.3 trillion in Department of Defense transactions were unaccounted for. The Secretary of Defense said to a roomful of media and officials that these missing assets were a greater threat than terrorism. In making this announcement on September 10 2001, Rumsfeld’s timing was uncanny, because the enormity of the missing trillions was lost in the 9/11 mass media event. Rumsfeld could have called a press conference in mid-July 2001, when he appeared before US Congressional House Appropriations Committee, with the Chairman of the Joint Chiefs of Staff General Hugh Shelton, who had signed off on the Full Spectrum Dominance plan for a permanent American-led military empire. In making testimony for ‘Defense Budget Requests’ for the coming year before the US Congressional House Appropriations Committee on July 16 2001, Rumsfeld downplayed this systemic audit failure, saying that the Department of Defense’s accounts were “snarled up”.
The chair of the House Appropriations Committee Rep. Lewis was flippant about the oversight of the unaccounted for transactions, stating that the matter could be talked about at another time. Given the magnitude of the breach, this was a remarkable dismissal of the matter. Rumsfeld responded, saying that the Comptroller of the Currency, Dov Zakheim, was looking into the audit failure situation and had “got a handle; it’s just a little hot”. Lewis burst into laughter and much of the room joined the chairman of the House Appropriations Committee in appreciating the in-joke, including Zakheim, who was chuckling as he sat beside Rumsfeld.
Zakheim, who was also member of the Project for a New American Century, had been CEO of System Planning Corporation (1987-2001), a company that developed Flight Termination Technology. This technology was successfully tested before 9/11, including the take-over of a Federal Express 727 jet. Flight Termination Technology made it possible to take over commercial airliners by remote control, effectively rendering pilots as helpless front-seat passengers. Ostensibly, the technology was developed to counter hijackings.
The immediate cover-up of the terror attacks that began on September 11 2011, together with the official account of 9/11, read like deep state criminal satirists scripted them. Those black satirists are likely to be Ryan’s 9/11 suspects. When it is also learned that the CIA-backed Mujahideen were the predecessor ‘freedom fighters’ to Al Qaeda, we begin to see the traces of a deep state network still at-large. And when the investigations of experts independent of the state apparatus are taken into account, the evidence leads to the reasonable conclusion that a network of deep state criminal actors were integral to making the terrorism of 9/11 more spectacularly successful than what 19 hapless ‘hijackers’ with box-cutters could have made it.
The ‘Al Qaeda’ ‘hijackers’ served as the gullible patsies.
No place to hide from cyber-carpetbaggers?
To those who know this Shock Doctrine history, it was no surprise that the NSA and GCHQ had spied on world leaders from the G20 industrial nations, as revealed by the Snowden leaks.[52] Nor would it have been a surprise for those that have tracked the development of the Echelon spy network, such as James Bamford and Nicky Hager, that major companies had descended down the Five Eyes’ rabbit hole, helping the NSA and GCHQ collect data on their respective mass populaces.

But, the news did not lesson the disturbing ramifications for those who understand and care about the importance of being able to peacefully contest the growing concentration and merger of state and corporate power by the transnational capital class. For such individuals, groups and institutions, the intrusive capacity of the Five Eyes’ states to eavesdrop on private conversations, remotely attend private meetings, and analyze internal organizational communications, it is a critical development that signals a major affront to the defence of free and open societies.
How can people effectively gather to hatch ideas, develop frameworks and coordinate strategies to challenge the wrongdoing perpetrated by the super-rich, that has become so evident amid a five-year long deepening global depression, if the Five Eyes’ states ‘get the jump’ every time? Indeed, former constitutional lawyer and Guardian reporter Glenn Greenwald, who broke Edward Snowden’s story, stated while promoting his new book, No Place to Hide: Edward Snowden, the NSA, and the U.S. Surveillance State, the NSA would like everyone to just think it only has ‘bad people’ in its sights.[53] Greenwald argues that it is the nature of those who head powerful institutions to defend power interests and that translates into spying on dissenting groups that are deemed a threat because they are effective at communication, mobilization and challenging injustices.[54] Greenwald argues that the NSA has trained its personnel to target what the government regards as “radicals”, a broad term to describe people who oppose the politically, economically and militarily powerful of the United States.

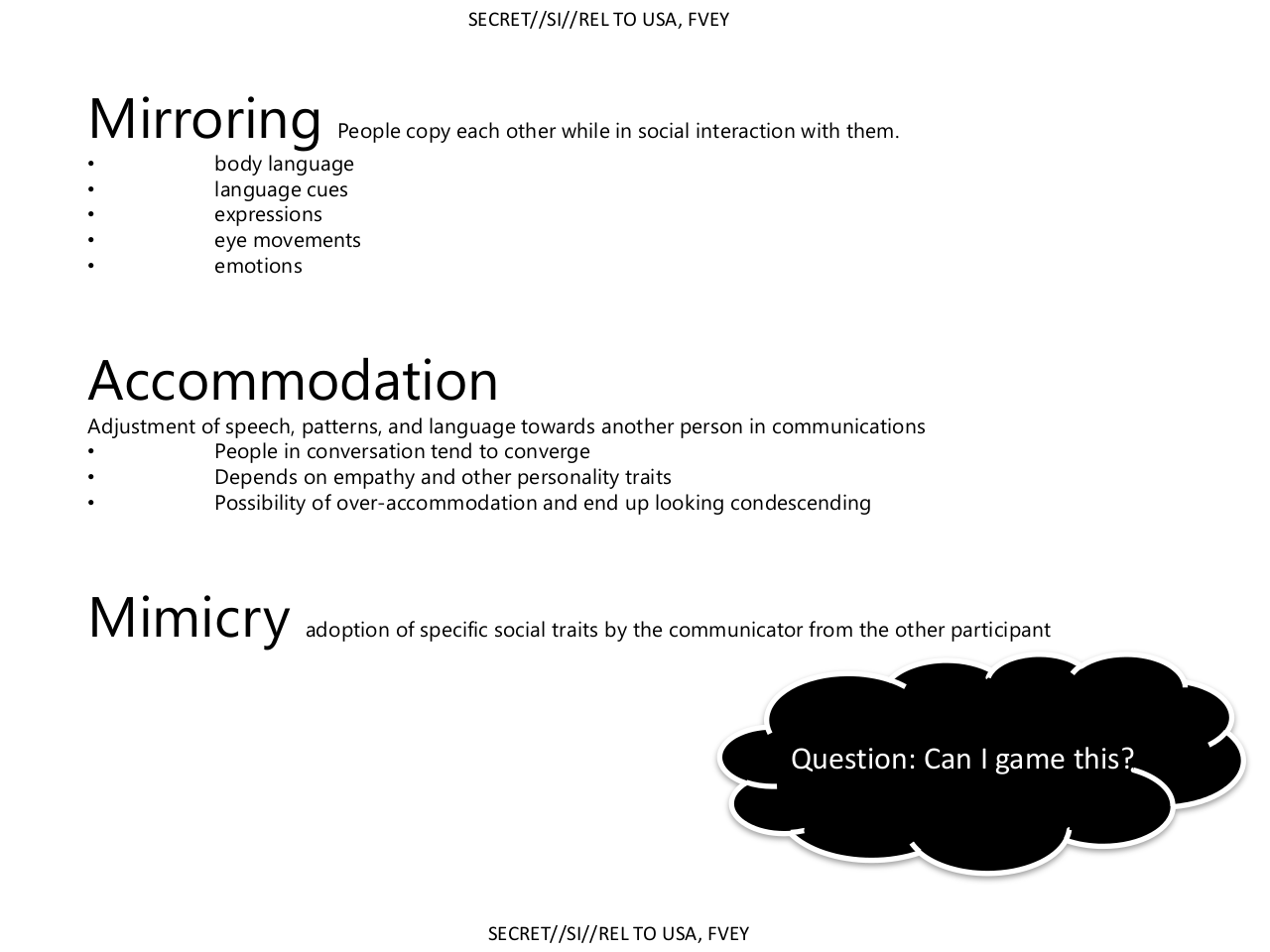
Furthermore, Greenwald revealed last year that the NSA’s British counterpart, the GCHQ, has trained its personnel to infiltrate activist groups online, to undermine their credibility, create internal division, and disrupt their communications.[55] The intention of the Government Communications Headquarters (GCHQ) was to circumvent the limitations of the law by using these powerful technologies and the cover of secrecy to attack groups that dissent against the United Kingdom’s government and that of its Anglo-Saxon Five Eyes spy partners. As Greenwald made clear, the GCHQ is targeting groups and individuals that have not been charged or convicted of any criminal offenses.
Adding weight to this argument that the Echelon network is at least as much about undermining home-grown dissent as it is about playing geopolitical chess, the NSA’s codeword for its decryption program, “BULLRUN”, is taken from two major battles of the American civil war. BULLRUN is the successor program to a prior decryption program called “MANASSAS”, that refers to the more conventional name for the two battles at Bullrun. These are potent names for the American people, because the US government realized the war was going to be a long hard-fought one since their forces lost the first major battle between the two armies in Manassas in 1861. In a second major battle at nearby Bullrun, Union forces won a decisive victory against the Southern Confederate opponents in 1862. Its British decryption counterpart, “EDGEHILL”, is named after the first major engagement of the English civil war, the Battle of Edgehill, of 1642, that was a shock to the Royalists fighting for the monarchy against the landed oligarchy’s parliamentary forces. It ended as an inconclusive “bloody draw”.[56] Thus, the names chosen for these decryption programs indicate that the top spooks of the Five Eyes’ global surveillance system had the stifling of domestic dissent in mind. Encoded as they are with symbolism of civil wars, these names used by both spy agencies also shows a commitment to advance ‘the game’ together, as cartel game theory predicts.[57]
Gaming the People
The five states that comprise the Five Eyes’ global spy apparatus are constructing a totalitarian super-state (or Transnational Corporate Empire), by stealth. A Fraternity in these institutions are linked to the ‘deep state’ that was responsible for Operation Gladio, and other acts of terror conducted by the US-NATO Alliance. It is this ‘deep state’ network that were key to the 9/11 plot.
Following the terrorism of September 11 2001, the NSA wasted no time increasing its capacity for mass surveillance and the US government stretched the law to make it seem legal. Numerous legal experts, including lawyers at the US Department of Justice, stated in the PBS documentary, United States of Secrets, that the White House and Justice Department deliberately subverted the 4th Amendment of the US Constitution. Because the 4th Amendment prohibits unlawful searches and seizures, and requires a warrant from a judge, these legal experts say that mass surveillance of the US population is unlawful.
In a brazen attempt to protect itself from a backlash, the NSA rides on its creation myth that says it was formed to prevent another ‘Pearl Harbor’. But, a trip to the Library of Congress to read a copy of Robert Stinnett’s meticulously researched book Day of Deceit: The Truth about FDR and Pearl Harbor, would collapse this myth that the Japanese attack on Pearl Harbor was a surprise. Likewise, if NSA staff and outsourced contractors would only read the various books cited here about American banking and industrial corporations that traded with the Nazis prior to and throughout World War II, the NSA’s worker spy bees would realize that numerous dynastic families of America head a criminal Fraternity.
The NSA-led global surveillance system is designed to serve us all up on platters, to feed the deep political interests of the richest cliques of pinstriped fascists the planet has known.[58] It is critical that their breaches of the Universal Declaration of Human Rights are confronted before democratic institutions are stripped of their vital functionality.[59]
While the US and UK news media has been critical of their respective governments in regard to the NSA’s and GCHQ’s mass surveillance, they are yet to provide the broader context that is touched upon here. This is in no small part because key insiders of the major media outlets have attended the Bilderberg meetings, kept them secret and manipulated the world’s mass populaces to serve the plans of North Atlantic capitalist class (now a transnational in scope), as Daniel Estulin’s book The True Story of the Bilderberg Group shows. Furthermore, key insiders of the major media outlets have also played an active role in other global-policy shaping groups such as the Council on Foreign Relations and the Trilateral Commission. It is not surprising, therefore, that the major media outlets have failed to conduct sustained serious investigations into the event that justified the expansion of NSA surveillance, and one that key insiders wasted no time capitalizing on: 9/11.
After-all, the mainstream media (MSM) still reproduces the fiction that Pearl Harbor was a surprise.
Almost 13 years after 9/11, the major media have barely begun to scratch the surface of the ‘deep state’. This is in spite of the fact that much credible evidence has been presented to them. Thousands of experienced people from diverse backgrounds such as: aviation and construction professionals, former and current officials, intelligence professionals, military officers, scientists, structural engineers and architects, and legal scholars, independent researchers, journalists and filmmakers are critical of the official 9/11 narrative. This deficiency is in spite of some early efforts by the mainstream media to investigate 9/11, amid the conspicuous absence of an authentic reflexive response from US authorities into their culpability.
The major Anglo-American media outlets are pulling their punches due to their institutional ties to the US and UK states and other major US and UK-based transnational corporations. Therefore, it is also crucial that we defend our minds from the psychological warfare (or Psy-Ops) emanating from the White House-Pentagon-CIA-NSA-GCHQ-Wall Street-City of London-Hollywood-News Propaganda-Think Tank Complex. Because just six US-based global media conglomerates – Time Warner, Disney, NewsCorp, NBC Universal, CBS and Viacom – dominate the USA America and world propaganda media system – they are able to present a relentless barrage of subterfuge as black and white truth, with near-impunity.[60] News is a serialized black satire. News commentary, as black satire, regularly deploys doublethink.
As readers familiar with George Orwell’s dystopian novel Nineteen Eighty-four will recall, doublethink is defined as “the power of holding two contradictory beliefs in one’s mind simultaneously, and accepting both of them” (1993 [1949]: 223). This brainwashing provides the capacity to dispense with unwelcome truths by forgetting them, yet being able to recall them when convenient and deliberately deceive others while maintaining an inner conviction that the choices are right. Henry Kissinger is committed to the idea of larger and larger political units being formed out of conflicts, like the three super-states described in Nineteen Eighty-four, because he is in the orbit of the American Rockefeller banking and oil dynasty. Like other deep state criminal actors among the Transnational Capitalist Class, David Rockefeller and Henry Kissinger have been long-associated with the global policy-shaping groups, such as the Council on Foreign Relations, the Trilateral Commission and the Bilderberg Group, that seek a one-world invisible government endgame (as numerous investigators have found). These investigations include: Daniel Estulin’s The True Story of the Bilderberg Group; James Perloff’s The Shadows of Power; Laurence Shoup and William Minter’s Imperial Brain Trust; William Engdahl’s A Century of War: Anglo-American Oil Politics and the New World Order; Michel Chossudovsky’s The Globalization of Poverty and the New World Order; and Jason Bermas’ Invisible Empire: A New World Order Defined.
Therefore, Snowden’s leaks have revealed power crimes, to a point. In response to the leaks, that reveal the construction of a global surveillance state, numerous high placed people have been forced to acknowledge that the US National Security Agency began conducting mass surveillance on US citizens following 9/11, as shown in the PBS documentary, United States of Secrets. Thus, these admissions to subvert the 4th Amendment of the US Constitution and Article 12 of the Universal Declaration of Human Rights come with the justification that the terrorism of September 11 2001 made the almost unlimited expansion of surveillance necessary. However, the bubble gum-free history of United States-sponsored terrorism sketched here shows that the United States of America is afflicted with a ‘deep state’ criminal network that crosses the corporate-state apparatus. This deep state criminal network are masters of mass deception since they were able to get whole populations to disbelieve their eyes and ears in regard to the 9/11 coup, and instead go along with a narrative wherein the laws of physics did not work properly on September 11 2001. Therefore, such ‘power crimes’ are the ‘big picture’ context that is missing in the news coverage of Edward Snowden’s leaks of the Five Eyes spy network, so far.
Multi-disciplinary investigations of power crimes can determine whether or not there is collusion or conspiracy underpinning current or historical events. Such investigations require studying the power relations of those that control or seek to control power resources. Conspiracies are secret agreements for political gain through the infliction of harm on society. With collusion, the goal is for economic gain.[61] Both frequently overlap. Conspiracy and collusion require propaganda to hide their planning, existence and history, particularly with large-scale projects.
Elite criminals who practice fraud, corruption and terrorism, argues professor of international law Eric Wilson, “optimize” their power and prestige through the construction of networks that work to minimize the risks of detection and maximize the payoffs [62]. By exploiting speed, criminal elites and oligarchs are able distort perceptions about the facts of events and why they occur. Thus, “low velocity political deliberation and public accountability” is overtaken by high-velocity events created by highly-networked private interests. It is in this way, that “politics ‘disappears into aesthetics’ ” – as Eric Wilson puts it. In this process, the splicing of space and time and kinetic image sequences mask “speed-politics” with a copy of reality. Thus, the mainstream media (MSM), acting as ‘vectors’ or transmitters of ‘emotional contagion’, assist the ‘speed-politics’ that underpin such ‘crises,’ amid an ‘atmosphere of catastrophe.’
The real value of power crime scholarship lays in the findings, which can reveal ‘deal breakers’ for society. If it became common knowledge that key power institutions have been manufacturing our consent for projects that have hidden purposes, societies would rightly revolt against the authorities, and redeploy key insiders to those institutions most suited to their actions: the prisons of the world’s Incarceration Complex.
Confronting the Construction of a Totalitarian Super-State
USA America, the nation state that leads the project to transform the American Empire into a Transnational Corporate Empire, is famous for boasting it’s accomplishments. But, it is coy about leading this project to construct a totalitarian super-state via a covert global neo-colonial project.
The United States has so much going for it. It has the best media propaganda system. Media cartels with profit autism busily reproduce syndicated Bubble Gum TV News History for Hollywood to reconstruct reality. USA America is so good at manufacturing consent. Also, in the ‘going for it’ stakes, USA America’s state-sponsored terrorism is ‘state of the art’. This makes the American Empire formidable because frightened mass populaces often do not realize who exactly is victimizing them. The US ‘deep state’, responsible for the expression of this violent fascist aesthetic, must surely gloat in private about their horrific work that we see daily on ‘the news’.
USA America has the very best mass surveillance system in the world. Indeed, it’s leading spy agency, the NSA, is so busy snooping on everyone’s private lives that it has not found the time or will to read up on the ‘deep state’ of the United States. It is sticking to its creation myth, when a stroll to the Library of Congress to read Day of Deceit: The Truth about FDR and Pearl Harbor, would collapse this myth that Japan’s attack on Pearl Harbor was a surprise. The NSA applies this ‘default setting’ to all the critical books cited in this investigation because, as a vital part of America’s ‘deep state’ apparatus, the NSA would be breaking ranks if it did otherwise. If more personnel and outsourced contractors connected to the American state apparatus did break ranks, all hell would break loose, no matter how much propaganda America’s anti-competitive media cartels throw at the truth.
Why? Because even totalitarian states are susceptible to fatal losses of legitimacy. The propaganda has to be relentless to sucker the gullible. The surveillance has to be total to deter the suspicious who can still think and to catch dissenting thoughtcriminals. And terrorism, including torture, is needed to scare everyone into submission.
When Black Things Propel Us
Ultimately though, it’s an impossible system to maintain. Why?
Because the power of love is universal. Love sets people free in the most unlikeliest, unpredictable and spontaneous of ways. Even in totalitarian super-states, where so much resource is committed to control. By infusing projects that educate, provoke and inspire bona fide freedom, the potent creative energy of love has the power to win over weak hearts to be brave ones.

Masses of people will come to see that it is psychopaths who run the world, when they realize that they have glimpsed the deepest fear of the powerful thousands of times. Ironically, their most guarded fear is that they are scaredy-cat cowards. Psychopaths project confidence to win the trust of their intended victims. Their power lays with exploiting secret knowledge and intent. In other words, psychopaths must maintain the perception that they are kind people, otherwise their power over others will collapse.
Thus, the ‘penny will drop’ that the myriad cover-ups, the denials upon denials, the forced resignations, the back-peddling, and the changing justifications, that we continue to see on ‘the news’ are the tell-tale signs of their cowardice. These ‘delete’, ‘force quit’ and ‘backspace’ moves are also evidence that deceit is the covert currency of high-conspiring powers. When critical masses of people see that conspiracy, collusion and corruption is systemic, they will realize that the love that binds ordinary people constitutes the real bonds with which to rebuild community.
Individually, people will feel propelled to find the resolve to brave an authentic life because their realizations about the black satire that the ‘deep state’ orchestrates will repulse them.
=====================
STORY MIRRORED: “When Black Things Propel Us: ‘Deep State’ Power Crimes” at http://snoopman.wordpress.com/2014/06/11/deep-state-power-crimes/
=====================
By day, Snoopman works undercover as an ordinary mortal, editing news at a television station. By night, Snoopman researches the wicked deeds of the powerful. The Snoopman News website (https://snoopman.net.nz/) publishes well-researched, referenced and fully-illustrated articles that investigate power-crimes (conspiracies for political power and collusion for economic gain).
SEE Snoopman News for Sources and Pictures
Shortlink: https://snoopman.net.nz/?p=1002
Facebook: Snoopman News https://www.facebook.com/pages/Snoopman-News/1406959546221223?ref=br_rs
Twitter: Snoop Monster @SnoopmanNews
SOURCES:
[1] Goodman, Amy. (2014, May 13). “Collect It All”: Glenn Greenwald on NSA Bugging Tech Hardware, Economic Espionage & Spying on U.N. Retrieved from http://www.democracynow.org/2014/5/13/collect_it_all_glenn_greenwald_on?autostart=true&get_clicky_key=suggested_related; Greenwald, Glenn & MacAskill, Ewen. (2013, June 11). Boundless Informant: the NSA’s secret tool to track global surveillance data. The Guardian. http://www.theguardian.com/world/2013/jun/08/nsa-boundless-informant-global-datamining; Greenwald, Glenn. (2013, July 31). XKeyscore: NSA tool collects ‘nearly everything a user does on the internet’. The Guardian. Retrieved from http://www.theguardian.com/
[2] United Nations. (2014). Universal Declaration of Human Rights of 1948. Retrieved from http://www.un.org/en/documents/udhr/
[3] Burghardt, Tom. (2013, November 10). The U.S. Secret State and the Internet: “Dirty Secrets” and “Crypto Wars” from “Clipper Chip” and ECHELON to PRISM. Global Research. Retrieved from http://www.globalresearch.ca/the-u-s-secret-state-and-the-internet-dirty-secrets-and-crypto-wars-from-clipper-chip-to-prism/5357623
[4] Daily Mail Reporter. (2013, September 6). NSA and GCHQ unlock encryption programs that EVERYONE uses to email and make purchases on their phones and tablets. Daily Mail. Retrieved from http://www.dailymail.co.uk/news/article-2413436/Edward-Snowden-leaks-NSA-GCHQ-unlock-encryption-programs-EVERYONE-uses.html; James Ball, Julian Borger and Glenn Greenwald (2013, September 6). Revealed: how US and UK spy agencies defeat internet privacy and security. The Guardian. Retrieved from http://www.theguardian.com/world/2013/sep/05/nsa-gchq-encryption-codes-security; Pelroth, Nicole, Larson, Jeff & Shane, Scott. (2013, September 5). N.S.A. Able to Foil Basic Safeguards of Privacy on Web. The New York Times. Retrieved from http://www.nytimes.com/2013/09/06/us/nsa-foils-much-internet-encryption.html?_r=0
[5] Greenwald, Glenn & MacAskill, Ewen. (2013, June 7). NSA Prism program taps in to user data of Apple, Google and others. The Guardian. Retrieved from http://www.theguardian.com/world/2013/jun/06/us-tech-giants-nsa-data; Hopkins, Nick. (2013, June 7). UK gathering secret intelligence via covert NSA operation. The Guardian. Retrieved from http://www.theguardian.com/technology/2013/jun/07/uk-gathering-secret-intelligence-nsa-prism; Glenn Greenwald, Ewen MacAskill, Laura Poitras, Spencer Ackerman and Dominic Rushe. (2013, July 12). Microsoft handed the NSA access to encrypted messages. The Guardian. Retrieved fromhttp://www.theguardian.com/world/2013/jul/11/microsoft-nsa-collaboration-user-data
[6] Greenwald, Glenn. (2013, July 31). XKeyscore: NSA tool collects ‘nearly everything a user does on the internet’. The Guardian. Retrieved from http://www.theguardian.com/
[7] Spying on Americans, Cellphones, Emails: The NSA is on the Line – All of Them. Retrieved from http://www.globalresearch.ca/spying-on-americans-cellphones-emails-the-nsa-is-on-the-line-all-of-them/5343442; WashingtonsBlog. (2013, June 24). The SINGLE Most Important Step to Protect Yourself from Government Spying. Retrieved from http://www.washingtonsblog.
[8] WashingtonsBlog. (2013, September 28). NSA’s Spying On Metadata Violates Our Freedom of Association. Global Research. Retrieved from http://www.globalresearch.ca/nsas-spying-on-metadata-violates-our-freedom-of-association/5351947
[9] Goodman, Amy. (2014, May 13). “Collect It All”: Glenn Greenwald on NSA Bugging Tech Hardware, Economic Espionage & Spying on U.N. Retrieved from http://www.democracynow.org/2014/5/13/collect_it_all_glenn_greenwald_on?autostart=true&get_clicky_key=suggested_related; Gellman, Barton & Poitras, Laura. (2013, June 7). U.S., British intelligence mining data from nine U.S. Internet companies in broad secret program. The Washington Post. Retrieved from http://www.washingtonpost.com/investigations/us-intelligence-mining-data-from-nine-us-internet-companies-in-broad-secret-program/2013/06/06/3a0c0da8-cebf-11e2-8845-d970ccb04497_story.html?Post+generic=%3Ftid%3Dsm_twitter_washingtonpost
[10] James Ball, Luke Harding and Juliette Garside. (2013, August 2). BT and Vodafone among telecoms companies passing details to GCHQ. The Guardian. Retrieved from http://www.theguardian.com/business/2013/aug/02/telecoms-bt-vodafone-cables-gchq
[11] Black, Edwin. (2012). IBM and the Holocaust: The Strategic Alliance Between Nazi Germany and America’s Most Powerful Corporation. Washington D.C.: Dialog Press. SEE ALSO: Black, Edwin. (2009). Nazi Nexus: America’s Corporate Connections to Hitler’s Holocaust. Washington D.C.: Dialog Press; Elston, P. (1998). Banking with Hitler. [Motion picture]. London: BBC; Engdahl, W. (2004). A Century of War: Anglo-American Oil Politics and the New World Order (Rev. ed.). London, England: Pluto Press; Engdahl, F. W. (2009). Gods of Money: Wall Street and the Death of the American Century. Wiesbaden, Germany: edition.engdahl; Higham Charles (1983). Trading with the Enemy: The Nazi-American Money Plot 1933-1949 (1983). Delacorte Press; Preparata, Guido Giacomo. (2005). Conjuring Hitler: How Britain and America Made the Third Reich. London: Pluto Press; Sutton, Anthony (2002). Wall Street and the Rise of Hitler. San Pedro, CAL: GSG & Associates.
[12] Gilmore, Jim (Producer), Kirk, Michael (Producer, Director & Writer), Wiser, Mike (Producer & Writer). (2014, May 13). United States of Secrets. Part I: The Program. Frontline. PBS. Retrieved from http://www.pbs.org/wgbh/pages/frontline/united-states-of-secrets/; Goodman, Amy. (2014, May 13). “Collect It All”: Glenn Greenwald on NSA Bugging Tech Hardware, Economic Espionage & Spying on U.N. Retrieved from http://www.democracynow.org/2014/5/13/collect_it_all_glenn_greenwald_on?autostart=true&get_clicky_key=suggested_related; Greenwald, Glenn (2014). No Place to Hide: Edward Snowden, the NSA, and the U.S. Surveillance State. London, UK: Hamish Hamilton. Madsen, Wayne. Washington Spies on NATO; Other Allies. Strategic Culture Foundation. Retrieved from http://www.strategic-culture.org/pview/2014/05/18/washington-spies-on-nato-other-allies.html
[13] Engdahl, F. W. (2009). Gods of Money: Wall Street and the Death of the American Century. Wiesbaden, Germany: edition.engdahl; Estulin, D. (2009). The True Story of the Bilderberg Group, 183-184. (North American Union ed.). Walterville, OR: Trine Day LLC. Shoup, L. H. & Minter, W. (2004 [1977]). Imperial Brain Trust: The Council on Foreign Relations and United States Foreign Policy, 254-284. New York, NY: Authors Choice Press.
[14] Gilmore, Kirk, & Wiser. (2014, May 13). United States of Secrets. Part I: The Program. PBS.
[15] Stinnett, Robert (2001). Day of Deceit: The Truth About FDR and Pearl Harbor. New York: NY. Touchstone Books; Pearl Harbor Review- Pearl Harbor. National Security Agency/Central Security Service. Retrieved from http://www.nsa.gov/about/cryptologic_heritage/center_crypt_history/pearl_harbor_review/pearl_harbor.shtml
[16] Chomsky, N. (2004). Hegemony or Survival: America’s Quest for Global Dominance. NSW, Australia: Allen & Unwin; Chomsky, N. (2006). Failed States: The Abuse of Power and the Assault on Democracy. Crows Nest, NSW: Allen & Unwin; Jarecki, Eugene (2006). Why We Fight. [Motion Picture]. Sony Pictures Classics; Klein, Naomi. (2007). The Shock Doctrine: The Rise of Disaster Capitalism. Camberwell, Australia: Penguin Books; Nazemroaya, Madhi Darius. (2012). The Globalization of NATO. Atlanta, USA: Clarity Press; Pilger, John. (2007). The War on Democracy. Retrieved from http://www.maoritelevision.com/tv/shows/tuesday-festival-documentaries; Pilger, J. (2002). The New Rulers of the World. London: Verso; Pilger, J. & Lowry, A. (2001). The New Rulers of the World. Carlton Television; Whitecross, M & Winterbottom, A. (Directors) & Eaton, A. (Producer). (2009). The Shock Doctrine. [Motion picture]. A Renegade Pictures/Revolution Films Production. Retrieved from http://www.youtube.com/watch?v=7iW1SHPgUAQ; Wintonick, P. (Director/Producer) & Achbar, M. (Director/Producer). (1992). Manufacturing Consent: Noam Chomsky and the Media [Motion picture]. Canada: Necessary Illusions.
[17] Bureau d´Études (2009). Bureau d´Études publishes new network map: Administration of Terror. Operation Gladio: Studies of NATO stay-behind networks and other clandestine resurgence operations. Retrieved from http://operation-gladio.net/bureau-d%C2%B4%C3%A9tudes-publishes-new-network-map-administration-terror; Nazemroaya, Madhi Darius (2012). The Globalization of NATO. Atlanta, Georgia, USA: Clarity Press.
[18] Webster Tarpley’s 9/11 Synthetic Terror; Alex Jones’ Terrorstorm (2010).
[19] Golinger, Eva. (2014, March 5). Colored Revolutions: A New Form of Regime Change, Made in the USA. Global Research. Retrieved from http://www.globalresearch.ca/colored-revolutions-a-new-form-of-regime-change-made-in-the-usa/27061; Marshall, Andrew Gavin (2009, November 3). Colour-Coded Revolutions and the Origins of World War III. Global Research. Retrieved from http://www.globalresearch.ca/colour-coded-revolutions-and-the-origins-of-world-war-iii/15767; Meyssan, Thierry. (2012, August 7). Perfecting The Method of “Color Revolutions”. Global Research. Retrieved from http://www.globalresearch.ca/perfecting-the-method-of-color-revolutions/32261; Muhho, Sam (2014, April 28). Color Revolutions. Getting Our Facts Straight on the “Arab Spring”. Global Research. Retrieved from http://www.globalresearch.ca/color-revolutions-getting-our-facts-straight-on-the-arab-spring/5379479
[20] Carroll, W. K. (2010). The Making of a Transnational Capitalist Class: Corporate Power in the 21st Century. London: Zed Books; Coghlan, Andy & MacKenzie, Debora Revealed – the capitalist network that runs the world. (2011, October 24). Retrieved from http://www.newscientist.com/article/mg21228354.500-revealed–the-capitalist-network-that-runs-the-world.html#.U4PmmoXelcw; Hedges, Chris. (2014, January 6). The Last Gasp of American Democracy. Truthout. Retrieved from http://www.truth-out.org/opinion/item/21052-chris-hedges-the-last-gasp-of-american-democracy; Edwards, Steve. (2012). It’s the financial oligarchy, stupid. Retrieved from http://hdl.handle.net/10292/5536; Phillips, Peter & Osborne, Brady (2013, September 13). Exposing the Financial Core of the Transnational Capitalist Class. Retrieved from http://www.globalresearch.ca/exposing-the-financial-core-of-the-transnational-capitalist-class/5349617; Phillips, Peter & Soeiro, Kimberley. (2012, August 14). The Global 1%: Exposing the Transnational Ruling Class. Retrieved from http://www.globalresearch.ca/the-global-1-exposing-the-transnational-ruling-class/32356
[21] Shoup & Minter. (1977). Imperial Brain Trust.
[22] Klein. (2007). The Shock Doctrine; Pappas, R. K. (Director/Writer), Blackburn, T. (Writer), Foley, M. (Producer). (2004). Orwell Rolls in his Grave [Motion picture]. USA: Buzzflash.com;
[23] de Angelis, M. (2001, May). Global capital, abstract labour, and the fractal panopticon. The Commoner. Retrieved from http://www.commoner.org.uk/fractalpanopt.pdf; Klein. (2007). The Shock Doctrine; Shoup & Minter. (1977). Imperial Brain Trust.
[24] Engdahl, F. W. (2009). Gods of Money: Wall Street and the Death of the American Century, p. 273-378 Wiesbaden, Germany: edition.engdahl; Estulin, D. (2009). The True Story of the Bilderberg Group, 137-147. (North American Union ed.). Walterville, OR: Trine Day LLC; Meyssan, Thierry. (2011, May 9). Voltaire Network.org. What you don’t know about the Bilderberg-Group. Retrieved from http://www.voltairenet.org/article169651.html
[25] Gosling, Tony. (2014, May 17). The World’s Most Powerful Private Club, Bilderberg’s Silent Takeover of Britain’s $60bn Defense Budget. Retrieved from http://www.globalresearch.ca/the-worlds-most-powerful-private-club-bilderbergs-silent-takeover-of-britains-60bn-defense-budget/5382698; Jones, Alex. (2010). Terrorstorm. Prison Planet.com; Marshall, Andrew Gavin. (2011, June 16). Bilderberg 2011: The Rockefeller World Order and the “High Priests of Globalization” Global Research. Retrieved from http://www.globalresearch.ca/bilderberg-2011-the-rockefeller-world-order-and-the-high-priests-of-globalization/25302; Meyssan, Thierry. (2011, May 9). What you don’t know about the Bilderberg-Group. Voltaire Network. Retrieved from http://www.voltairenet.org/article169651.html; Nazemroaya, Mahdi Darius. (2012). The Globalization of NATO. Clarity Press.
[26] Committee on Banking, Currency and Housing. (1976). Staff Report of the Committee on Banking, Currency, and Housing, House of Representatives, 94th Congress, Second session, May 1976; Estulin 2009). The True Story of the Bilderberg Group, p.137.
[27] Klein (2007). The Shock Doctrine. p. 78.
[28] Engdahl 2009: 273-275; Estulin 2009: vi, 137, 142, 145-146; Klein 2007; Shoup & Minter 1977: 254-281).
[29] Estulin 2009; Klein 2007; Shoup & Minter 1977: 254-281.
[30] Knight Frank & Citi Private Bank (2012). The Wealth Report 2012: A global perspective on prime property and weath. Knight Frank LLP & Citi Private Bank, Citigroup Inc. Retrieved from http://www.thewealthreport.net/The-Wealth-Report-2012.pdf; Pattel, Raj. (2013). Stuffed and Starved: From Farm to Fork – The Hidden Battle for the World Food System. Portobello Books.
[31] Wood, Patrick (2011a, January 26). Carbon Currency: A New Beginning for Technocracy? The August Forecast and Review. Retrieved from http://www.augustforecast.com/2010/01/26/carbon-currency-a-new-beginning-for-technocracy/; Wood, Patrick. (2010, March 3) “Smart Grid: The Implementation of Technocracy?” The August Forecast and Review. Retrieved from http://www.augustforecast.com/2010/03/03/smart-grid-the-implementation-of-technocracy-2/; Wood, Patrick. (2011b, June 15). Technocracy’s Endgame: Global Smart Grid. The August Forecast and Review. Retrieved from http://www.augustforecast.com/2011/06/15/technocracys-endgame-global-smart-grid/
[32] Estulin 2009; Klein 2007.
[33] Rockefeller John D. III. The Second American Revolution. New York: Harper & Row. In: Engdahl, F. W. (2009). Gods of Money: Wall Street and the Death of the American Century, p.275. Wiesbaden, Germany: edition.engdahl
[34] Gardner, Richard. (1974, July). Hard Road to World Order. Foreign Affairs. As cited in Estulin (2009: 83).
[35] Brzezinski, Zbigniew (1969). Between Two Ages: America’s Role in the Technetronic Era. Viking Press.
[36] Estulin 2009: 93-94.
[37] Brown, E. H. (2008). The Web of Debt: The Shocking Truth About Our Money System and How We Can Break Free (2nd ed.). Baton Rouge, LA: Third Millennium Press; Griffin, G. E. (2008). The Creature from Jekyll Island: A Second Look at the Federal Reserve (4th ed.). Westlake Village, CA: American Media; Grignon, P. (2009). Money as Debt II: Promises Unleashed. Retrieved from http://www.moneyasdebt.net/; Hutchinson, F. (1998). What Everyone Really Wants To Know About Money. Charlbury, England: Jon Carpenter; Nitzan, J. & Bichler, S. (2009). Capital as Power: A Study of Order and Creorder. New York, NY: Routledge; Palan, R., Murphy, R., & Chavagneux, C. (2010). Tax Havens: How Globalization Really Works. Ithaca, NY: Cornell University Press; Quigley, C. (1966). Tragedy and Hope: A History of the World in Our Time, p.37. New York, NY: The Macmillan Company; Rowbotham, M. (1998). The Grip of Death: A Study of Modern Money, Debt Slavery and Destructive Economics. Charlbury, England: Jon Carpenter; Shaxson, N. (2011). Treasure Islands: Uncovering the Damage of Offshore Banking and Tax Havens. New York, NY: Palgrave Macmillan; Winters, J. A. (2011). Oligarchy. New York: Cambridge University Press.
[38] Edwards, Steve. (2012). It’s the Financial Oligarchy, Stupid: A study of Anglo-American news coverage during the 2007-2008 financial crisis and bank bailouts. AUT University. Retrieved from http://aut.researchgateway.ac.nz/handle/10292/5536; Klein (2007). The Shock Doctrine; Whitecross & Winterbottom. (2009). The Shock Doctrine. [Motion picture]. A Renegade Pictures/Revolution Films Production. Retrieved from http://www.youtube.com/watch?v=7iW1SHPgUAQ
[39] Chomsky (2006: 111). Failed States.; Jarecki (2002). The Trials of Henry Kissinger. BBC; Klein (2007: 60, 63-70, 128). The Shock Doctrine.
[40] These oil price shocks, which were orchestrated by the Rockefeller’s Standard Oil cartel and Henry Kissinger (in collusion with the Bilderberger Group), set off an inflationary period around the world. Mohammad Reza Pahlavi, better known as the Shah of Iran, was induced to buy US-made weaponry, but he lacked the cash. The Rockefeller-Kissinger-Bilderberger nexus worked out that they needed a trigger event that would work as a cover for the Shah of Iran to hike oil prices so that he could afford his military spending. Kissinger, with the assistance of ‘back channels’ in London, orchestrated the Yom Kippur War of 1973 by deceiving the Egyptians, Syrians and Israeli’s about each others’ agendas. The ensuing oil embargoes meant that countries were forced to pay 400% more for petroleum, which was traded in US dollars, amid the reduced supply of oil. In turn, this meant that Wall Street banks, especially Rockefeller’s Chase Manhattan Bank made enormous profits. The Chase Manhattan Bank was the Iranian government’s bank, as well as the bank of the National Iranian Oil Company and also the Shah’s family bank Thus, the world was subjected to a far-reaching shock treatment that served the Anglo-American oligarchy’s interests. (Engdahl 2004: 127-141; 2009: 265-272); A Century of War; Engdahl 2009: 265-275). Gods of Money; Estulin (2009: 46). The True Story of the Bilderberg Group.
[41] Ruppert, Michael C. (2004). Crossing the Rubicon – The Decline of the American Empire. New Society Publishers; Ryan, Kevin. (2013). Another Nineteen: Investigating Legitimate 9/11 Suspects. USA: Microbloom; Scott, Peter Dale. (2012, September 24). “Systemic Destabilization in Recent American History: 9/11, the JFK Assassination, and the Oklahoma City Bombing.” The Asia-Pacific Journal, Vol 10 Issue 39, No. 2. Retrieved from http://japanfocus.org/-Peter_Dale-Scott/3835; Scott, Peter Dale. (2014, April 6). “The American Deep State, Deep Events, and Off-the-Books Financing,” The Asia-Pacific Journal, Vol. 12, Issue 14, No. 3. Retrieved from http://www.japanfocus.org/-Peter_Dale-Scott/4104; Tarpley, Webster Griffin. (2007). 9/11 Synthetic Terror: Made in USA. Joshua Tree, CAL: Progressive Press; Scott, Peter Dale. (2013, April 27). 9/11, the JFK Assassination, and the Oklahoma City Bombing as a Strategy of Tension. Voltaire Network. Retrieved from http://www.voltairenet.org/article178312.html; Unwelcome Guests Radio. (2013, December 10). Peter Dale Scott on The US War Machine (Deep Politics and the CIA Global Drug Connection). Retrieved from https://www.youtube.com/watch?v=MDUByvD25HI
[42] Avery, Dylan. (2007). Loose Change: Second Edition and Final Cut. loosechange911.com; Fetzer, James H. (Ed.). (2007).The 9/11 Conspiracy: The Scamming of America. Peru, Illinois, USA: Catfeet Press; Gage, Richard. (2008). 9/11: Blueprint for Truth. Architects and Engineers for 9/11 Truth. http://www.AE911truth.org; Henshall, Ian & Morgan (2005). 9/11 Revealed – Challenging Facts Behind the War on Terror. London: Robinson; Smallstorm, Sophia. (2007). Demolitions: 9/11 Mysteries. http://www.9/11weknow.com; Thompson, Paul et al. “The Complete 911 Timeline Project.” Cooperative Research History Commons http://www.historycommons.org/project.jsp?project=911_project
[43] 9/11: Blueprint for Truth. Architects and Engineers for 9/11 Truth. Retrieved from http://www.AE911truth.org
[44] Global Research. (2009, April 3). Active Thermitic Material Discovered in Dust from the 9/11 World Trade Center Catastrophe. Retrieved from http://www.globalresearch.ca/active-thermitic-material-discovered-in-dust-from-the-9-11-world-trade-center-catastrophe/13049; Hoffman, Jim (2009, December 7). Explosives Found in World Trade Center Dust. 9-11 Research. Retrieved from http://911research.wtc7.net/essays/thermite/explosive_residues.html; Ryan, Kevin. (2013, December 9). 9/11 Truth: How to Debunk WTC Thermite at Ground Zero. Global Research. Retrieved from http://www.globalresearch.ca/how-to-debunk-wtc-thermite/5360964; Ryan, Kevin R., Gourley, James R., Jones, Steven E. (2009, March). Environmental anomalies at the World Trade Center: evidence for energetic materials. The Enviromentalist, Volume 29, Issue 1, pp 56-63. Retrieved from http://download.springer.com/static/pdf/406/art%253A10.1007%252Fs10669-008-9182-4.pdf?auth66=1401059195_7b8d418b40be8a9c2abd135526f545ee&ext=.pdf
[45] Henshall, Ian. (2007). 9/11 Revealed: The New Evidence . New York: Carroll & Graf Publishers.
[46] Tarpley, Webster Griffin. (n.d.). The 46 Drills, Operations, War Games, And Activities Of 9/11. Retrieved from tarpley.net/docs/drills_of_911.pdf; Wilson, E. (2009). Speed/pure war/power crime: Paul Virilio on the criminogenic accident and the virtual disappearance of the suicidal state. Crime, Law & Social Change, 51, 413-434. doi:10.1007/s10611-008-9168-7
[47] Donnelly, Thomas, Kagan, Donald & Schmitt, Gary (2000). “Rebuilding America’s Defenses: Strategy, Forces and Resources for a New American Century” Part V Creating Tomorrow’s Dominant Force. A Report of The Project for a New American Century. Retrieved from http://web.archive.org/web/20070807020846; Shelton, General Henry H. (2000, June). “Joint 2020 Vision – America’s Military: Preparing for Tomorrow.” US Government Printing Office; Washington: DC.
[48] Gilmore, Jim (Producer), Kirk, Michael (Producer, Director & Writer), Wiser, Mike (Producer & Writer). (2014, May 13). United States of Secrets. Part I: The Program. Frontline. PBS. Retrieved from http://www.pbs.org/wgbh/pages/frontline/united-states-of-secrets/
[49] Donnelly, Kagan & Schmitt, Gary (2000). “Rebuilding America’s Defenses”, p. 51. Retrieved from http://web.archive.org/web/20070807020846
[50] Engdahl, F. William. (2011). Full Spectrum Dominance: Totalitarian Democracy in the New World Order. California, USA: Progressive; Right Web, Profiles – Individuals, Organizations, Governments. (n.d.). Project for a New American Century. Retrieved from http://www.rightweb.irc-online.org/list_of_pnac_signatories_and_contributing_writers
[51] Ryan, Kevin. (2013). Another Nineteen: Investigating Legitimate 9/11 Suspects. SEE ALSO: Ryan, Kevin. (2009, August 9). Demolition access to the WTC Towers. Retrieved from http://www.911review.com/articles/ryan/demolition_access_p1.html; Dell, Thomas. (n.d.). L. Paul Bremer. NNDB: Tracking the entire world. Retrieved from http://www.nndb.com/people/289/000023220/
[52] Ewen MacAskill, Nick Davies, Nick Hopkins, Julian Borger and James Ball (2013, June 17). GCHQ intercepted foreign politicians’ communications at G20 summits. The Guardian. Retrieved from http://www.theguardian.com/uk/2013/jun/16/gchq-intercepted-communications-g20-summits; Ewen MacAskill & Borger, Julian. (2013, June 30). New NSA leaks show how US is bugging its European allies. The Guardian. Retrieved from http://www.theguardian.com/world/2013/jun/30/nsa-leaks-us-bugging-european-allies
[53] Goodman, Amy. (2014, May 13). “Collect It All”: Glenn Greenwald on NSA Bugging Tech Hardware, Economic Espionage & Spying on U.N. Retrieved from http://www.democracynow.org/2014/5/13/collect_it_all_glenn_greenwald_on?autostart=true&get_clicky_key=suggested_related
[54] James Ball, Luke Harding and Juliette Garside. (2013, August 2). WashingtonsBlog. (2014, May 15). Spying is Meant to Crush Citizens’ Dissent, not Catch Terrorists. Retrieved from http://www.globalresearch.ca/spying-is-meant-to-crush-citizens-dissent-not-catch-terrorists/5382374; WashingtonsBlog. (2014, January 9). 500 Years of History Shows that Mass Spying Is Always Aimed at Crushing Dissent. Retrieved from http://www.washingtonsblog.com/2014/01/government-spying-citizens-always-focuses-crushing-dissent-keeping-us-safe.html.
[55] Greenwald, Glenn. (2014, February 24). How Covert Agents Infiltrate the Internet to Manipulate, Deceive, and Destroy Reputations. The Intercept. Retrieved from https://firstlook.org/theintercept/2014/02/24/jtrig-manipulation/
[56] CWSAC Battle Summaries: Manassas, First. (n.d.). National Park Service. Retrieved from http://www.nps.gov/hps/abpp/battles/va005.htm; CWSAC Battle Summaries: Manassas, Second. (n.d.). National Park Service. Retrieved from http://www.nps.gov/history/hps/abpp/battles/va026.htm; UK Battlefields Resource Centre. (n.d.). Battle of Edgehill 23rd October 1642. Battlefields Trust. http://www.battlefieldstrust.com/resource-centre/medieval/battleview.asp?BattleFieldId=3
[57] Ayres, I. (1987). How Cartels punish: A structural theory of self-enforcing collusion. Columbia Law Review, 87(2), 295-325. Retrieved from http://www.columbialawreview.org; Katyal, N. K. (2002). Conspiracy theory. The Yale Law Journal, 112, 1307-1398. Retrieved from http://yalelawjournal.org/; Marcus, P. (1977). Conspiracy: The criminal agreement, in theory and practice. The Georgetown Law Journal, 65, 925-969. Retrieved from http://www.georgetownlawjournal.org/; Marks, R. D. (1986). Can conspiracy theory solve the “oligopoly problem”? Maryland Law Review, 45, 387-431. Retrieved from http://www.law.umaryland.edu/academics/journals/mdlr/
[58] Carroll, W. K. (2010). The Making of a Transnational Capitalist Class: Corporate Power in the 21st Century. London: Zed Books; Chossudovsky, Michel. (2014, January 29). Imperial Conquest: America’s “Long War” against Humanity. Global Research. Retrieved from http://www.globalresearch.ca/imperial-conquest-americas-long-war-against-humanity/5364215; Lendman, Stephen. (2013, July 19). US Courts Approve Indefinite Detention and Torture. Global Research. Retrieved from http://www.globalresearch.ca/us-courts-approve-indefinite-detention-and-torture/5343269; Lendman, Stephen. (2013, November 12). America’s Global Gulag: Challenging Wrongful Convictions Global Research. Retrieved from http://www.globalresearch.ca/americas-global-gulag-challenging-wrongful-convictions/5357796?print=1; Perloff, J. (2008). The Shadows of Power: The Council on Foreign Relations and the American Decline. Appleton, WI: Western Islands; Phillips, Peter, Osborne, Brady (2013, September 13). Exposing the Financial Core of the Transnational Capitalist Class. Retrieved from http://www.globalresearch.ca/exposing-the-financial-core-of-the-transnational-capitalist-class/5349617; Phillips, Peter, Thornton, Bridget & Vogler, Celeste (2010, May 2). The Global Dominance Group: 9/11 Pre-Warnings & Election Irregularities in Context Retrieved from http://www.projectcensored.org/the-global-dominance-group/; Snoopman. (2014, March 10). “Code Purple: Whistle Blowing on ‘Free markets’, the ‘Shock Doctrine’ and ‘New Constitutionalism’” Snoopman News. Retrieved from at https://snoopman.net.nz/2014/03/10/code-purple/; WashingtonsBlog. (2013, December 18). Former Top NSA Official: “We Are Now In A Police State”. Retrieved from http://www.washingtonsblog.com/2013/12/former-top-nsa-official-now-police-state.html; Winters, J. A.(2012, February 27). Oligarchy in the U.S.A.: The wealth defense industry protects the richest of the rich. In These Times. Retrieved from http://inthesetimes.com/article/12698/oligarchy_in_the_u.s.a/; World Socialist Web Site. (2013, December 18). “Almost Orwellian”: US Judge indicts NSA spying. Retrieved from http://www.wsws.org/en/articles/2013/12/18/pers-d18.html
[59] United Nations. (2014). Universal Declaration of Human Rights of 1948. Retrieved from http://www.un.org/en/documents/udhr/
[60] SEE Chapter 3 of: Edwards, Steve. (2012). It’s the financial oligarchy, stupid: A study of Anglo-American news coverage during the 2007-2008 financial crisis and bank bailouts. Retrieved from http://hdl.handle.net/10292/5536; Goodman, Amy. (2014, May 14). Glenn Greenwald: U.S. Corporate Media is “Neutered, Impotent and Obsolete”. Democracy Now! Retrieved from http://www.democracynow.org/2014/5/14/glenn_greenwald_us_corporate_media_is
[61] SEE Chapter 2 of: Edwards, Steve. (2012). It’s the financial oligarchy, stupid: A study of Anglo-American news coverage during the 2007-2008 financial crisis and bank bailouts. Retrieved from http://hdl.handle.net/10292/5536;
[62] Wilson, E. (2009). Speed/pure war/power crime: Paul Virilio on the criminogenic accident and the virtual disappearance of the suicidal state. Crime, Law & Social Change, 51, 413-434. doi:10.1007/s10611-008-9168-7; Wilson, E. (2010, February). Crimes against reality: The global credit crisis, simulation, and criminogenic cyber-capitalism. Paper presented at the International Studies Association Annual Convention, New Orleans, LA. Retrieved from International Studies Association website: http://convention2.allacademic.com/one/isa/isa10/; Wilson, E. (2011). Criminogenic cyber-capitalism: Paul Virlio, simulation, and the global financial crisis. Springer Science+Business Media. doi: 10.1007/s10612-011-9139-7.
=====================
Story Republished on Scoop News as: “When Black Things Propel Us: ‘Deep State’ Power Crimes” at: http://www.scoop.co.nz/stories/HL1409/S00152/when-black-things-propel-us-deep-state-power-crimes.htm (Shortlink: https://snoopman.net.nz/?p=1002)